
Micro-Segment Your Applications
Micro-segmentation removes implicit trust and ensures your applications are secure from lateral movement.
Stop Ransomware and Other Threats
Eliminate a common attack vector to keep ransomware and other threats from getting a foothold on your network.
Onboard New Apps and Users Quickly
Stand up new applications quickly and securely, easily enroll or decommission users and devices, and get insights into application status and usage.
Control Access to Apps and Data
Based On User Identity and Device Health
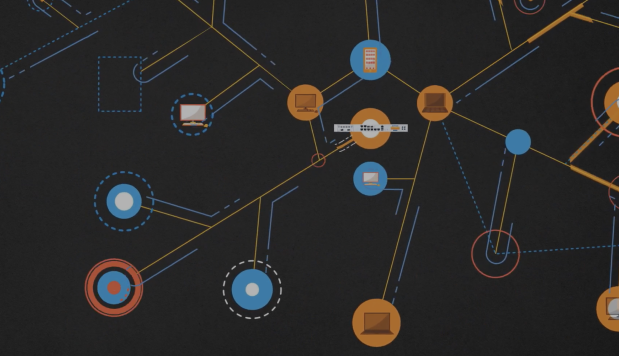
Sophos ZTNA delivers on the principles of zero trust: trust nothing, verify everything. Individual users and devices become their own micro-segmented perimeter that are constantly validated and verified. With zero trust, users are no longer “on the network” with all the implied trust and access that usually comes with it.
Trust is Earned, Not Given
Uniquely Integrated: ZTNA and Next-Gen Endpoint
Sophos ZTNA is the only zero trust network access solution that
is tightly integrated with a next-gen endpoint product – Sophos Intercept X.

End-to-End Protection
With Sophos ZTNA and Intercept X, you’re not just securing your application access, you’re also protecting your endpoints and network from Ransomware and other advanced threats with the most powerful machine learning and next-gen endpoint technology available. It’s holistic end-to-end protection that’s easier and more effective.
Synchronized Security
Sophos ZTNA and Intercept X are constantly sharing status and health information to automatically isolate compromised systems to prevent threats from moving or stealing data.
Single Agent, Single Console, Single Vendor
Sophos ZTNA and Intercept X are both part of the world’s most trusted cybersecurity ecosystem. They deploy together as a single client agent and are both managed together from Sophos Central. It’s a winning combination that you won’t find anywhere else.
Automatic Threat Response
Sophos ZTNA utilizes device health to automatically limit compromised devices from accessing business resources. It takes full advantage of its unique integration with the full Sophos ecosystem especially Sophos Intercept X endpoints.
Security Heartbeat
Share device health between Intercept X, Sophos Central, ZTNA, and Sophos Firewall in real time.
Automatic Threat Response
Compromised devices can have access automatically limited to isolate and contain threats, preventing lateral movement until they are cleaned up.
Deployment Alongside Intercept X
Get the world’s best endpoint protection and zero-trust network access with a single client deployment. No additional agents to install.
How Can We Help?
Whether you’re ready to speak with someone about pricing, want to dive deeper on a specific topic, or have a problem that you’re not sure we can address, we’ll connect you with someone who can help.
