Stop Reacting and Start Responding with Hexnode XDR
Cut through noise with a unified XDR solution; see everything, stop advanced threats, and empower your team to respond faster with precision.
Complex Threats. Simple Response.
Without XDR
Undetected Breach
Advanced malware evades signature-based Anti Virus, slipping through undetected.
Delayed Discovery
Teams spot breach post-damage, via ransom notes or outages, entry unclear.
Reactive Patchwork
No visibility means only wipes or restores, while the actual vulnerability remains.
With
Contextualized Alerts
Alerts auto-enriched with endpoint data, giving instant threat context.
Automated Correlation
Hexnode XDR links signals across your endpoints, revealing attacks end-to-end.
Coordinated Response
Hexnode XDR triggers instant multi-layer defence: isolate, kill or quarantine endpoints and files.
Orchestrate Endpoint Security
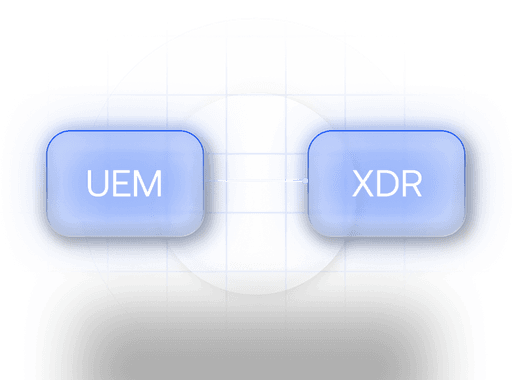
Hexnode UEM Integration
Hexnode: UEM & XDR as one. See threats, auto-remediate, patch fast, & slash MTTR.
One-Click Threat Remediation
Instantly isolate, kill and quarantine threats to stop breaches before they spread.
Complete Audit Trail
Every technician action and system event is immutably logged for total traceability.
Precision Threat Hunting
Cross-Platform Visibility
Secure and manage Windows and macOS environments from a single pane of glass.
The Modern XDR Toolkit
See Everything. Instantly.
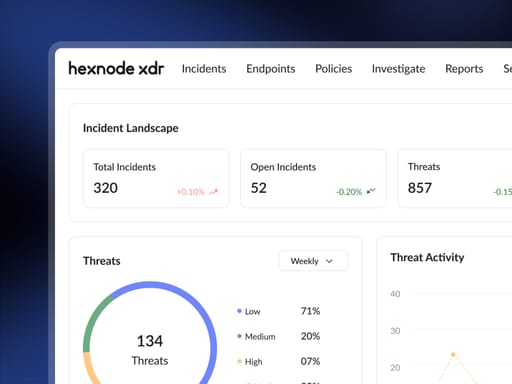
Unified Dashboard
Get a 360° real-time view of threats, active incidents, and endpoint health.
Threat Trends & Analytics
Threat trend visualisation to detect patterns and stop risks before they strike.
MITRE ATT&CK® Insights
Hexnode XDR maps threats to MITRE ATT&CK®, revealing motive and method.
Complete Device Vitals
Drill into any endpoint; see health, policies, and color-coded events.
Respond with Speed and Certainty
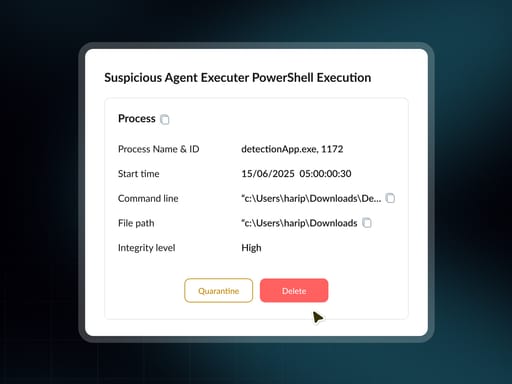
Isolate Device
One click cuts network access to devices, halts spread, and preserves control for forensics.
Kill Process
Kill malicious processes instantly on any endpoint with a single click.
Quarantine File
Safely contain malicious files, blocked, encrypted, and ready for review.
Deep Scan & Timely updates
Verify remediation with Deep scan for device health & other vital parameters.
Threat Hunt with Precision
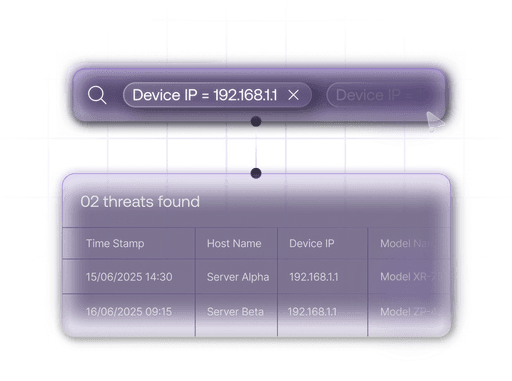
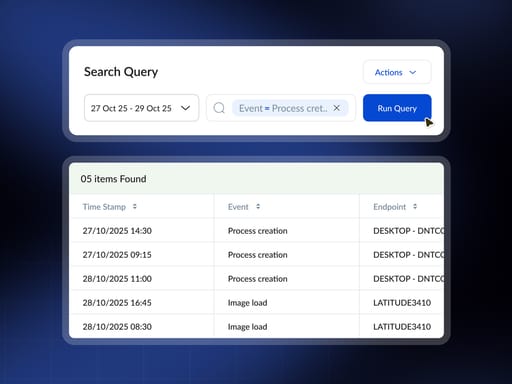
Intuitive Query Builder
Build complex queries with ease using search suggestions, recent history, and saved queries.
Advanced Investigation Query
Search 7 days of detailed endpoint data stored for instant access.
Efficient Query Workflow
Build, save, and share queries with a fast, intuitive interface.
Actionable Data Tables
View, filter, and export query results in a clean data table.
Put Your Security on Autopilot.
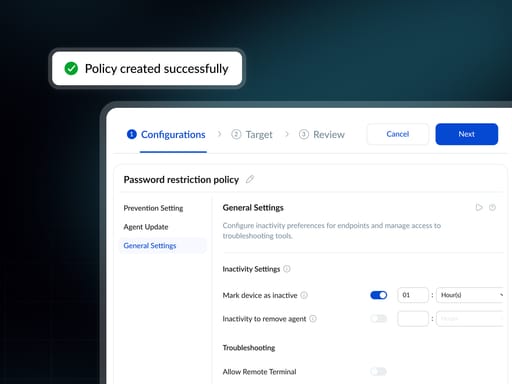
Smart Policy Lifecycle
Design, validate, and deploy robust security policies with ease.
Dynamic Endpoint Groups
Automate policy assignment with groups based on device criteria.
Custom Alert Profiles
Build fine-tuned alerts to eliminate noise and alert fatigue.
Seamless Agent Management
Keep agents updated and enable tamper protection automatically.